I noted in an October 2020 article that I have two SoloKeys – open source physical second-factor authentication devices based on the FIDO U2F API – to protect several compatible accounts. SoloKeys, and other physical authenticators generally work with Chromium-based web browsers, including my current primary and preferred browser, Ungoogled Chromium. I had experienced no issues using my SoloKeys on my desktop with Ungoogled Chromium as a second-factor authentication method for websites and applications for which it was enabled.
I had no problem, that is, until I tried to log into the Google account that I set up specifically to deal with certain issues pertaining to The New Leaf Journal.
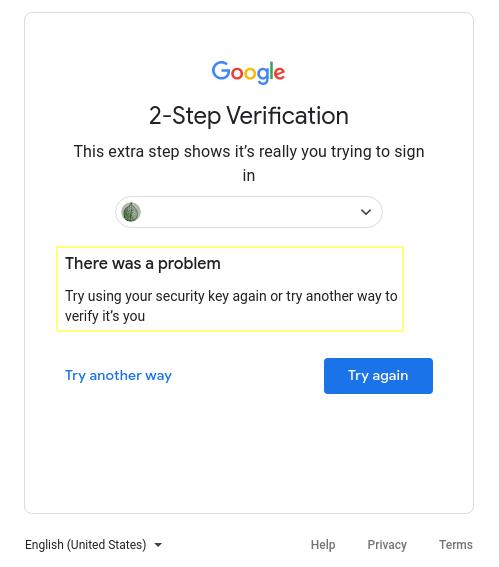
When I tried to log into my Google account, I received an error message informing me that there was an issue with my preferred second-factor authentication method. This was ultimately no problem – I have a second second-factor authentication method enabled (TOTP with Aegis Authenticator), but I was curious why my security keys did not work for logging into Google from Ungoogled Chromium.
I suspected that it had something to do with the ungoogled aspect of Ungoogled Chromium. Ungoogled Chromium is a fully open source web browser with its source code published on GitHub. Out of curiosity, I decided to check its GitHub repository page to see if my question would be answered.
Because Ungoogled Chromium is well-documented, it did not take me long to find the answer to my question. The following is quoted from the Ungoogled Chromium Wiki:
Google sign in uses a specific extension to access the security key’s information. You’ll need to install this extension to make this function. After installation you might need to restart your computer to make it work.
As I suspected, Google handles FIDO two-factor authentication different than other services that allow it do. July 31, 2023 Update: The extension referenced in my original article no longer works. There is no way to make Google sign-in work in Ungoogled Chromium as of July 31, 2023.
According to an April 2020 GitHub exchange between a user and the maintainer of Ungoogled Chromium (Eloston), the additional extension method may not always work. However, as the user opined (and I agree): “Unless this is someone[’s] only means of authenticating with Google, I would rank this as a low priority issue.”
I have no need to jump through the hoops since I have a suitable backup authentication method for Google that works in Ungoogled Chromium and all browsers (and because this issue only affects Google), but it was an interesting discovery nevertheless.
I conclude by offering my gratitude to Eloston and all the contributers to the Ungoogled Chromium browser for the hard work they put in to maintain a valuable project. For those who are interested in trying the Google-free version of Chromium, it is available for Windows, Mac, and Linux (some distributions have specific packages, others can use the Flatpak version). For any fellow users of an Arch-based distribution, I will append a note of caution that building the Arch User Repository version of Ungoogled Chromium is a RAM-intensive task.